File System Analysis: Unveiling the Secrets of Data Storage
In the vast digital landscape of today, file systems form the backbone of data storage and organization. From personal computers to enterprise-level servers, understanding how file systems work is crucial for maintaining data integrity, optimizing performance, and uncovering valuable insights. This is where file system analysis comes into play.
File system analysis involves examining the structure, metadata, and content of a file system to gain a comprehensive understanding of its intricacies. It goes beyond simply browsing folders or scanning files; it delves into the underlying architecture and uncovers hidden information that can be vital for various purposes such as forensic investigations, data recovery, or performance optimization.
One key aspect of file system analysis is understanding the file allocation methods used. Different file systems employ various techniques to allocate space for storing files on storage devices. Analyzing these allocation methods can reveal patterns in how files are stored and provide insights into fragmentation issues or potential optimizations.
Metadata plays a crucial role in any file system. It contains valuable information about files such as their names, sizes, creation dates, permissions, and much more. By analyzing metadata, we can reconstruct timelines of events or track changes made to files over time. This can be invaluable in forensic investigations or when trying to recover lost or deleted data.
Another important aspect of file system analysis is examining deleted or hidden data. When files are deleted from a storage device, they are not immediately erased; rather, their entries in the file system’s index are marked as available for reuse. Through careful analysis and specialized tools, it is often possible to recover deleted files or extract fragments of information that have been left behind.
File system analysis also enables us to identify anomalies or signs of malicious activity. By examining access logs or analyzing metadata inconsistencies, we can detect unauthorized access attempts or tampering with critical files. This plays a crucial role in digital forensics investigations and helps uncover evidence that may be crucial in legal proceedings.
Moreover, file system analysis helps optimize storage performance. By understanding how files are organized and stored, we can identify bottlenecks or inefficiencies in the system. This knowledge allows us to implement strategies such as defragmentation, compression, or data migration to enhance performance and ensure smooth operations.
In recent years, with the rise of cloud storage and distributed file systems, the importance of file system analysis has only increased. Analyzing distributed file systems helps us understand how data is replicated, distributed, and accessed across multiple nodes. This knowledge is essential for ensuring fault tolerance, data consistency, and efficient utilization of resources.
In conclusion, file system analysis is a powerful tool for unraveling the mysteries of data storage. It provides us with insights into the inner workings of file systems, helps recover lost or deleted data, detects anomalies or malicious activities, optimizes performance, and ensures the integrity of our digital assets. As technology continues to advance and more complex file systems emerge, mastering the art of file system analysis becomes increasingly crucial for IT professionals and digital investigators alike.
Commonly Asked Questions about File System Analysis in Digital Forensics and Cyber Security
- What is file in system analysis?
- What is file system in cyber security?
- What are the four steps of the forensic process?
- What is file system analysis in digital forensics?
What is file in system analysis?
In file system analysis, a “file” refers to a unit of data storage that is organized and managed by a file system. It is a logical entity that represents a collection of related information, such as text, images, programs, or any other type of data.
Files are the fundamental building blocks of any file system. They are typically identified by a unique name and are stored in directories or folders within the file system’s hierarchical structure. Each file has associated metadata, which includes attributes like file size, creation date, permissions, and other relevant information.
During file system analysis, files are examined to gain insights into their structure, content, and relationships within the file system. This analysis involves studying various aspects of files such as their allocation methods, metadata attributes, access patterns, and potential anomalies or inconsistencies.
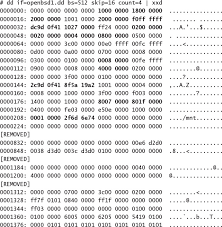
File system analysts often use specialized tools and techniques to extract valuable information from files. This can include examining the internal structure of specific file formats (e.g., analyzing the header or footer of an image file), recovering deleted files or fragments of data, identifying patterns in how files are organized or stored on storage devices (e.g., detecting fragmentation), or identifying signs of unauthorized access or tampering.
By analyzing files within a file system, analysts can reconstruct timelines of events (e.g., when a file was created or modified), track changes made to files over time, identify potential security breaches or data breaches through forensic investigations, optimize storage performance by identifying inefficiencies or bottlenecks in how files are stored or accessed, and gain insights into the overall organization and utilization of data within the file system.
In summary, files play a central role in file system analysis as they contain valuable information that can be extracted and analyzed for various purposes such as forensic investigations, performance optimization, data recovery, security assessments, and overall understanding of how data is organized within a given file system.
What is file system in cyber security?
In the realm of cybersecurity, a file system refers to the structure and organization of files on a storage device, such as a hard drive or a network server. It plays a significant role in ensuring data security and protecting against various cyber threats.
File systems in cybersecurity are responsible for managing access permissions, enforcing user authentication, and implementing encryption mechanisms to safeguard sensitive information. They provide the foundation for controlling how files are stored, accessed, and protected within an operating system or network environment.
Here are some key aspects of file systems in cybersecurity:
- Access Control: File systems incorporate access control mechanisms that determine who can access specific files or directories. By setting permissions and assigning user roles, organizations can restrict unauthorized individuals from viewing or modifying sensitive data.
- Encryption: File systems may offer encryption capabilities to protect files both at rest and during transmission. Encryption algorithms convert data into unreadable ciphertext, ensuring that even if an attacker gains unauthorized access to the files, they cannot decipher the information without the proper decryption key.
- Auditing and Logging: File systems often include auditing features that track file access events, modifications, or deletions. These logs provide valuable information for investigating security incidents, identifying potential breaches, or monitoring user activities for compliance purposes.
- File Integrity Monitoring: File system security tools can employ techniques like file integrity monitoring (FIM) to detect unauthorized changes to critical system files or configurations. FIM solutions compare file attributes against baseline values to identify any alterations that may indicate tampering or malware infection.
- Malware Detection: File systems play a crucial role in detecting and mitigating malware threats. Antivirus software scans files as they are accessed or downloaded from external sources to identify known malware signatures or suspicious behavior patterns.
- Data Recovery: In the unfortunate event of data loss due to cyberattacks or system failures, file systems often facilitate data recovery processes by utilizing backup mechanisms or employing specialized recovery tools.
- Secure Deletion: File systems may include secure deletion features to ensure that sensitive files are permanently erased from storage devices. This prevents unauthorized individuals from recovering deleted files and accessing confidential information.
Overall, file systems in cybersecurity encompass a range of security measures and functionalities designed to protect data, control access, detect threats, and ensure the integrity of files. By implementing robust file system security practices, organizations can enhance their overall cybersecurity posture and safeguard their critical assets from unauthorized access or malicious activities.
What are the four steps of the forensic process?
The forensic process typically involves four main steps:
- Collection: The first step in the forensic process is the collection of evidence. This involves identifying and preserving potential sources of evidence, such as computers, mobile devices, or other storage media. It is crucial to ensure that the evidence is collected in a forensically sound manner to maintain its integrity and admissibility in legal proceedings.
- Examination: Once the evidence is collected, it undergoes a thorough examination. This step involves analyzing the data and extracting relevant information using specialized forensic tools and techniques. The examination may include tasks such as file system analysis, keyword searches, data recovery, or decryption to uncover hidden or deleted information.
- Analysis: After the examination phase, the collected data is analyzed to draw conclusions or answer specific investigative questions. This step involves interpreting the findings from the examination, identifying patterns or anomalies, and forming hypotheses based on the available evidence. The analysis may require collaboration with subject matter experts or additional testing to validate findings.
- Reporting: The final step in the forensic process is documenting and presenting the findings in a clear and concise report. The report should include a detailed description of the investigation methodology, the evidence collected, analysis performed, and conclusions drawn. It should be prepared in a manner that can be easily understood by both technical and non-technical audiences.
It’s important to note that these steps are not always strictly linear and may require iteration or revisiting previous steps based on new discoveries or evolving investigative needs. Additionally, throughout the entire process, maintaining proper documentation and chain of custody is critical to ensure that all actions taken are well-documented and legally defensible if required in court proceedings.
What is file system analysis in digital forensics?
File system analysis in digital forensics is a specialized process that focuses on examining and extracting information from file systems to gather evidence for investigations. It involves analyzing the structure, metadata, and content of file systems on storage devices such as hard drives, solid-state drives (SSDs), or removable media.
In digital forensics, file system analysis plays a crucial role in uncovering valuable evidence that can be used in legal proceedings. Here are some key aspects of file system analysis in digital forensics:
- File Recovery: File system analysis allows forensic investigators to recover deleted or hidden files from storage devices. By examining the file system’s metadata and analyzing unallocated space, it is possible to reconstruct deleted files or extract fragments of data that may have been left behind.
- Timeline Reconstruction: By analyzing the timestamps embedded in the file system’s metadata, investigators can reconstruct timelines of events related to file creation, modification, or deletion. This helps establish a sequence of activities and provides a clearer understanding of the chronology of events.
- Metadata Examination: File system metadata contains valuable information about files such as their names, sizes, timestamps, permissions, and ownership details. Analyzing this metadata can provide insights into user activities, access patterns, or potential tampering with files.
- File Carving: File carving is a technique used in file system analysis to extract files from unallocated space or fragmented areas of storage devices. This process involves identifying file signatures or patterns within raw data and reconstructing complete files from these fragments.
- Link Analysis: By examining the relationships between files and directories within a file system, investigators can identify connections between different pieces of evidence. Link analysis helps establish associations between files or users and can be crucial for understanding how information was accessed or shared.
- Keyword Search: File system analysis allows investigators to perform keyword searches across file names, content, or metadata fields within a storage device. This helps identify files or documents relevant to the investigation and speeds up the process of finding specific information.
- Anomaly Detection: File system analysis enables the detection of anomalies or suspicious activities within a storage device. By analyzing access logs, metadata inconsistencies, or file system artifacts, investigators can identify unauthorized access attempts, file tampering, or attempts to hide information.
Overall, file system analysis in digital forensics is a fundamental process that helps investigators uncover evidence, reconstruct timelines of events, recover deleted files, and detect anomalies within file systems. It requires specialized tools and expertise to navigate through complex storage structures and extract valuable information that can be crucial in legal proceedings.
